Prepare For the Worst with the Best in the Business
Experience capable, consistent, and easy-to-use business continuity management software.
Why most residual risk statements fail under scrutiny
Most teams understand the difference between inherent and residual risk. That is rarely the issue. The problem shows up when those definitions are put under pressure.
Residual risk statements often look clean in a spreadsheet, but they are not built to be challenged. When audit or leadership asks how the rating was determined, the answer is usually incomplete. Controls are listed, but not tied to outcomes. Scenarios are implied, but not clearly defined. Timing is missing. Assumptions are hidden.
At that point, residual risk stops being a useful statement and becomes an opinion. That is why it fails under scrutiny.
Residual risk is not just a label. It is a claim about exposure after mitigation. And like any claim, it needs to be supported by logic, evidence, and context.
Inherent vs residual risk, grounded in practice
Inherent risk describes what happens if no controls exist. Residual risk describes what remains after controls are applied. That sounds straightforward, but the mistake is treating these as abstract scoring steps.
In practice, they are two versions of the same story. One describes the scenario without mitigation. The other describes how that scenario changes once controls are introduced. If the scenario itself is weak or unclear, both inherent and residual risk become unstable.
The quality of the risk statement depends less on the scoring scale and more on how clearly the underlying situation is described.
Example 1: Banking scenario under audit pressure
Consider a payment processing outage at a financial institution. A common version of the risk statement might describe inherent risk as critical, list a disaster recovery plan as the control, and assign a medium residual risk.
This looks reasonable until it is examined more closely. The control is documented, but there is no indication of whether it has been tested, how quickly systems can be restored, or whether dependencies have been validated. When audit asks for evidence, the team cannot point to anything beyond the existence of the plan.
A stronger version of the same scenario describes the situation in operational terms. The inherent risk is critical because transactions stop immediately. The controls include a documented disaster recovery plan, a completed failover test, and a validated secondary environment. The residual risk is then described in relation to time, with higher exposure in the first few hours and reduced exposure once failover is complete.
The difference is not complexity. It is the presence of evidence and timing. That is what makes the statement defensible.
Example 2: Healthcare scenario where assumptions break down
Now consider an electronic health record outage in a hospital environment. A typical statement might describe inherent risk as high, list downtime procedures as the control, and assign a low residual risk.
This fails for a different reason. It assumes that manual procedures can sustain operations without testing whether that is actually true under pressure. It also ignores the variability between departments and the impact on patient care when systems are unavailable for extended periods.
A stronger version of this scenario makes those assumptions visible. It describes inherent risk as critical because patient care begins to degrade quickly. It then explains that downtime procedures exist, that drills have been conducted, and that only certain departments have validated manual workflows. The residual risk reflects those limits, showing higher exposure in the early stages and reduced confidence as the duration increases.
By exposing limitations instead of hiding them, the statement becomes more credible rather than less.
Example 3: Technology scenario with overstated controls
A third example comes from a SaaS provider dependent on third-party infrastructure. Teams often describe the control as a service-level agreement and conclude that residual risk is low.
This is a common mistake. An SLA defines expectations, not capability. It does not reduce immediate impact or guarantee recovery in practice.
A more defensible statement separates contractual protection from operational readiness. It explains what failover options exist, what monitoring is in place, and how quickly service can realistically be restored. Residual risk is then described in relation to those capabilities rather than the existence of an agreement.
This shift from assumption to capability is what makes the difference under scrutiny.
What strong residual risk statements have in common
Across these examples, the pattern is consistent. Strong residual risk statements are built around a clear scenario, not a generic label. They describe controls in terms of what those controls actually enable. They connect outcomes to time, making it clear when disruption becomes unacceptable. They also acknowledge uncertainty instead of hiding it.
Weak statements tend to skip these steps and move directly to a rating. That is why they are easy to challenge.
How to pressure-test your own risk statements
A simple way to evaluate your own work is to ask how it would hold up in a conversation with audit or leadership. If you cannot clearly explain what the disruption looks like, how controls change that situation, and when impact becomes unacceptable, the statement will not hold.
This is less about adding more detail and more about making the logic explicit. When the reasoning is clear, the rating becomes easier to defend.
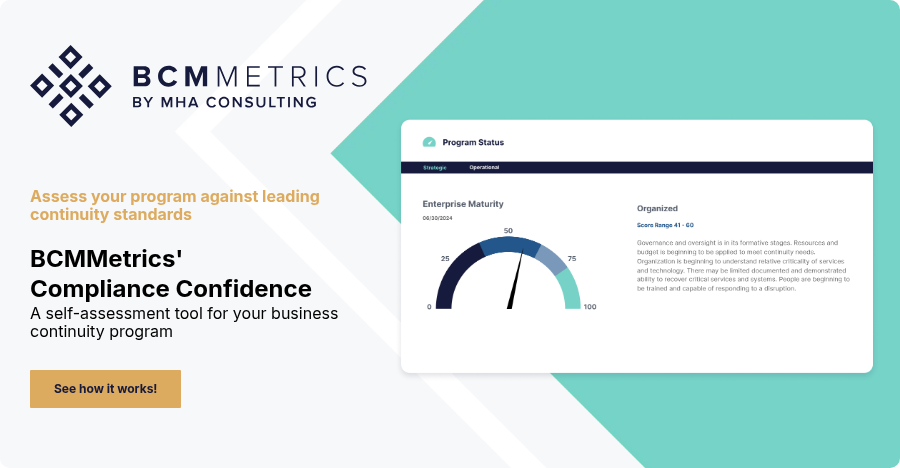
How this maps to tooling
As programs grow, maintaining this level of clarity becomes difficult when everything is stored in separate documents or spreadsheets. Differences in language, structure, and assumptions make comparison harder over time.
A structured approach helps maintain consistency. Tools such as Compliance Confidence support linking scenarios, controls, and evidence in a way that can be reviewed and validated. The benefit is not better reporting. It is the ability to defend decisions without rework.
FAQ
What is inherent risk?
Inherent risk is the level of exposure before any controls are applied.
What is residual risk?
Residual risk is the level of exposure that remains after controls are in place.
Why do residual risk statements fail in audit?
They fail because they lack clear linkage between scenario, controls, timing, and evidence.
How do you make residual risk defensible?
By making assumptions explicit and tying controls to measurable outcomes.
Related BCMMetrics Articles

Michael Herrera
Michael Herrera is the Chief Executive Officer (CEO) of MHA. In his role, Michael provides global leadership to the entire set of industry practices and horizontal capabilities within MHA. Under his leadership, MHA has become a leading provider of Business Continuity and Disaster Recovery services to organizations on a global level. He is also the founder of BCMMETRICS, a leading cloud based tool designed to assess business continuity compliance and residual risk. Michael is a well-known and sought after speaker on Business Continuity issues at local and national contingency planner chapter meetings and conferences. Prior to founding MHA, he was a Regional VP for Bank of America, where he was responsible for Business Continuity across the southwest region.
.png)
.png)